Like it or not, traditional passwords aren’t going away. In this article, I’ll share some best practices when creating a corporate password policy to save you and your organization some headaches.
Know what you’re looking for? Skip ahead:
TL;DR
- While the future could very well be passwordless, your organization still needs a corporate password policy today
- There is a lot of misleading and even flat-out wrong information about how to create a secure password
- The longer the password, the better. Passphrases are also a secure and effective alternative.
- You should never reuse or share passwords.
- Two-Factor Authentication (2FA) adds an additional layer of protection and should be used whenever possible.
Microsoft recently suggested that passwords have reached the end of their lifecycle.
That may be true, but this change isn’t going to happen overnight. The implementation of secure alternatives to standard logins will take a long time to adopt.
This leaves organizations with the unfortunate reality that, for now, passwords are here to stay.
Password policy no-nos
If you were to scour the web in search of recommendations for secure password policies, you would probably see a few common themes:
- Minimum of 8-12 characters
- A mix of upper case, lower case, numbers, and special characters
- Password rotation
- Account lockouts after 3-5 bad attempts
Great advice, or so it would seem. According to Beyond Trust, these policies are, “…at best, incomplete, and at worst, completely WRONG!… it is outdated, incomplete cybersecurity advice that was never actually good in the first place.”
So why do so many organizations consider these policies to be at the forefront of security? It boils down to habits. According to a survey performed by BitWarden, an organization known for its open-source password manager, 84% of people reuse passwords across multiple sites. Since we know it only takes one breach at the correct organization to compromise millions of username and password pairs, 84% is terrifyingly high. If we add to that the fact that most people recycle their security question pairs across sites, it becomes easy to see how vital it is to maintain a unique username and password pair.
With this in mind, here are a few tips and tricks when developing a corporate password policy to save you time, frustration, and potentially a lot of money.
How to create a great corporate password policy
Use longer passwords or a passphrase
While 8-12 characters are great, the longer the password can be, the better.
If a server allows you to set a 32-character password, do it. According to a NIST Special Publication 800-63-3, the best password practice is to generate passwords up to 64-characters long. We’re all in a hurry to get things done and the last thing we want to do is to memorize a 32-character password, but there are plenty of open-source, free, or pay-to-use password managers out there that integrate seamlessly with contemporary web browsers and/or have lightweight clients for PC/Mac.
Alternatively, you can also use a passphrase instead of a password. A random four-word passphrase (e.g., logic finite eager ratio) is easier to remember and virtually impossible to crack.
💡 What is password entropy?
Password entropy is the level of uncertainty associated with a password and is presented in bits. The higher the entropy value, the more secure the password is. Passwords that are not present in a list of 50,000 commonly used passwords have around 10 bits of entropy. Interestingly, a passphrase that consists of four random words with spaces between has around 40 bits of password entropy.
Regardless of whether you use the more obscure longer password or the passphrase, this step is vital.
Use Two-Factor Authentication (2FA) whenever possible
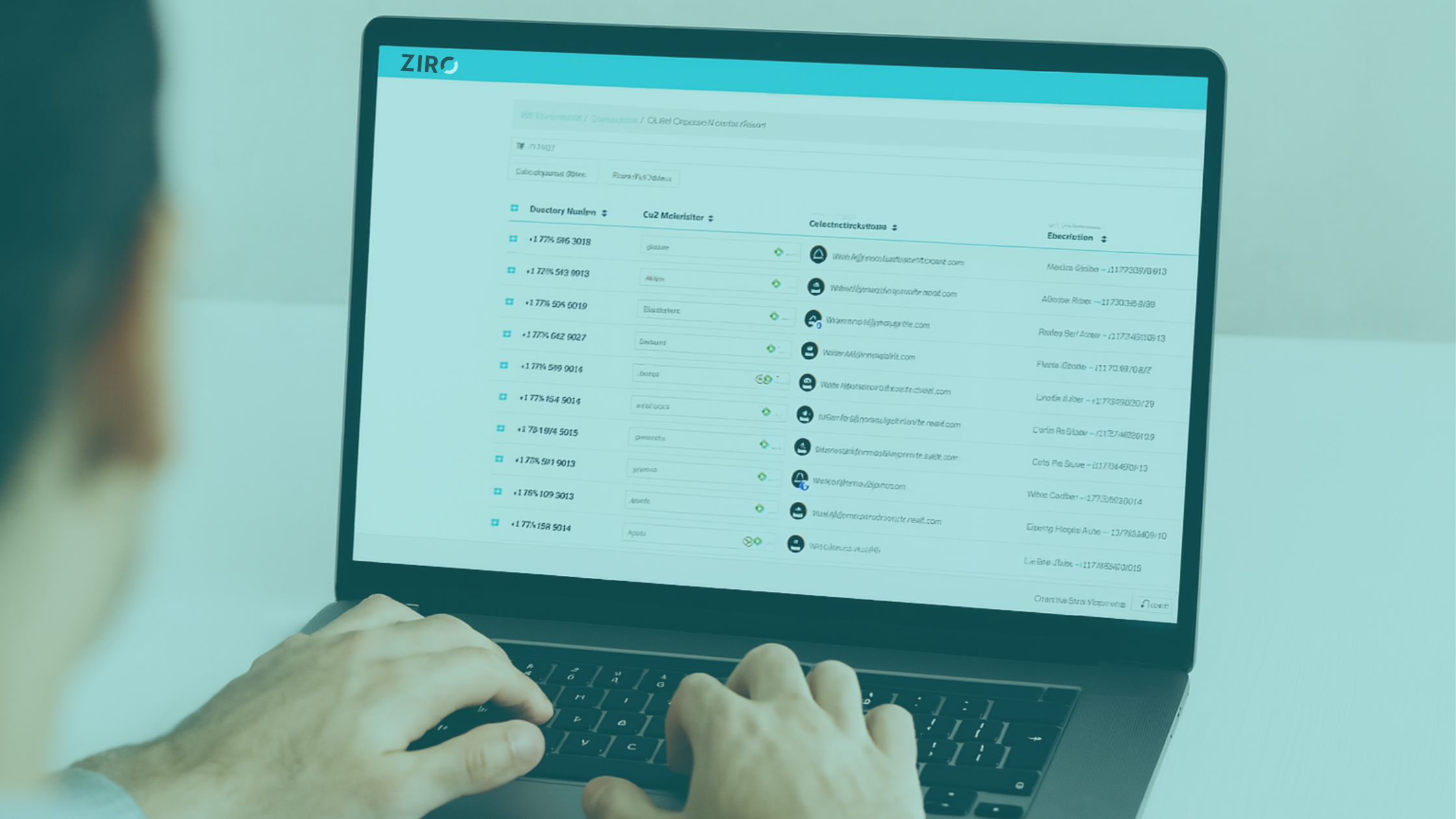
In addition to the 32 or 64-character password, 2FA requires the end user to acknowledge that they are the ones that are attempting to log in to a server. 2FA allows the end user to flag suspicious login attempts for review by your security team for threat assessment analysis.
Do not use dictionary words
As mentioned above, there are countless password managers available on the market today. Most come equipped with a feature to generate a secure password of a given length using character subsets. Utilize this password generator to create and store your personal and enterprise secure passwords.
Do not use the same password across sites or servers
While it may be more convenient to use the same password, it also opens your systems and information to attack by allowing the attacker access to multiple platforms with a single user-password pair. I see this often in organizations’ I.T. departments. It is critical to use separate passwords for each server/site. In the case of Windows-based servers, your domain credentials with 2FA are sufficient. The same would apply to switching infrastructure utilizing ACS or RADIUS and 2FA. However, in the case of databases and voice servers where the username and password can be different, they should be.
Don’t share passwords
Under no circumstance should passwords be shared. While it may be more convenient for John to give Mary his password so that she can get something done in a hurry, in doing so audit log tracing becomes more convoluted. This also includes sending passwords via email or unencrypted channels. Just don’t do it.
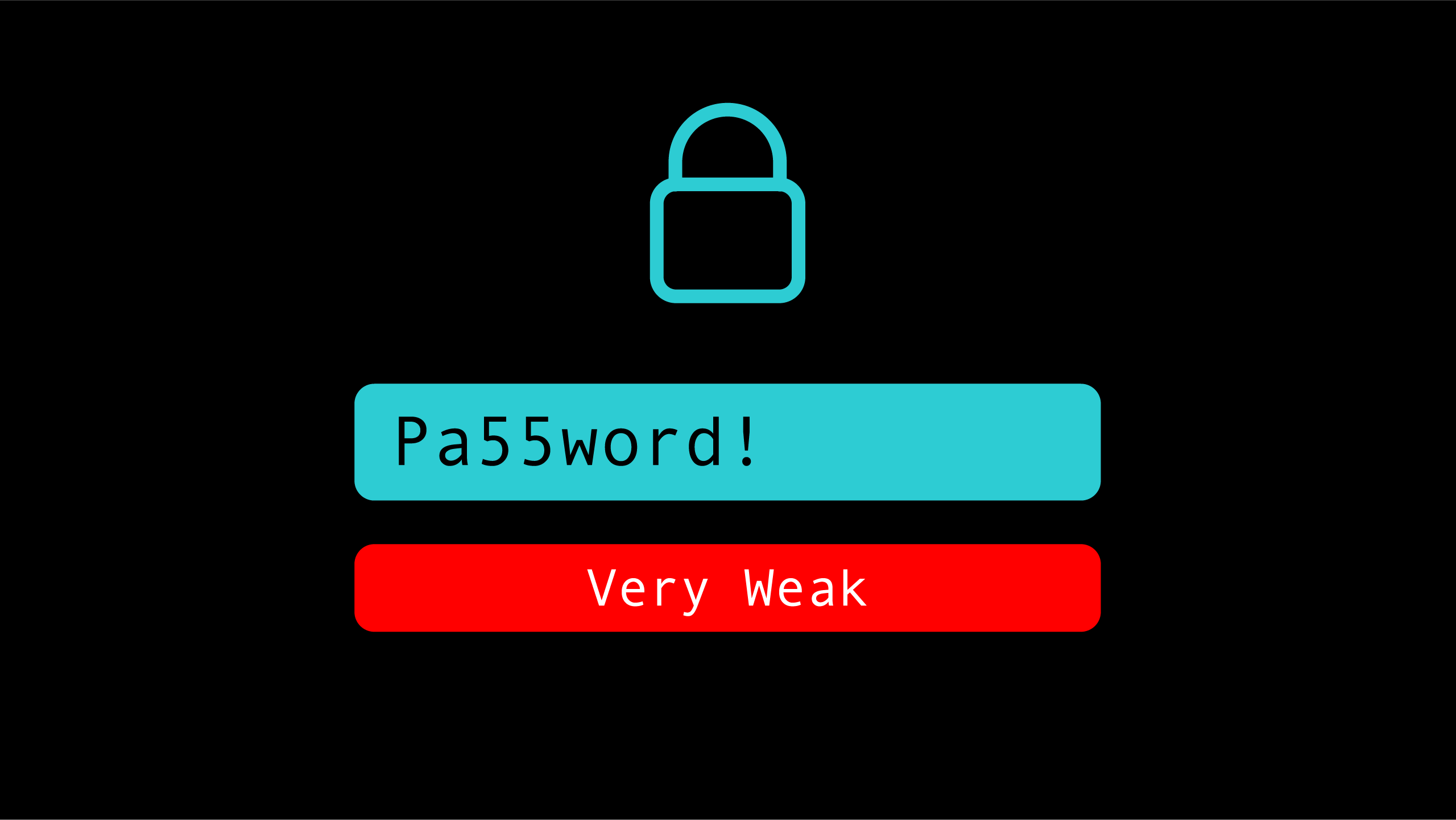
Avoid password rotation policies
Again, habit dictates that forcing users to change their passwords every 90 days means that they will have enhanced their secure footprint, practice shows us that those same users will simply add a bang “!” to the end of their already recycled password. This kind of password update doesn’t help them or the organization. Instead, enforce a strict password length and complexity policy and allow it to remain static. Provide password manager access to the end user so that they do not feel the need to try to memorize their credentials.
Final Thoughts
While they may be cumbersome to maintain, login pairs can be easily managed with the help of a password management application. The use of these tools by organizations allows for the peace of mind in knowing that passwords are both secure in length and complexity but are also not being recycled across the I.T. landscape. The addition of 2FA simply adds that bonus layer of protection empowering users to report suspicious login attempts to the appropriate teams.
By establishing these best practices, you’ll be able to create an effective corporate password policy and keep your organization secure. If you have any questions or need help managing your Microsoft Teams configuration, contact us today or call +1-844-940-1600.
Ready to take your unified communications from headache to hassle-free?
No throwing darts at proposals or contracts. No battling through the back-end. No nonsense, no run-around.